]]>
/*
先看看enum類的構(gòu)造函數(shù)
再來看調(diào)用過程
(transactionId, network) -> {
它是lamdba寫法,看看構(gòu)造函數(shù)需要一個 CommitHandlerFactory 接口,這個lamdba 函數(shù)其實就是CommitHandlerFactory 的實現(xiàn)。
這樣MSPID_SCOPE_ALLFORTX 枚舉類型就有了一個 CommitHandlerFactory實現(xiàn)類的引用。
再看create調(diào)用。
這里enum類的create方法會執(zhí)行, return factory.create(transactionId, network);
返回一個 CommitHandler .這里才會真正執(zhí)行那個 lamdba定義的函數(shù)。
到這里只看到lamdb應(yīng)用。。。
再分析一下create ,枚舉類里的每個枚舉變量都會實現(xiàn)一個這個方法。這里可以看到它其實是一個工廠類。
它創(chuàng)造的產(chǎn)品是CommitHandler ,其具體實現(xiàn)是CommitHandlerImpl類。
這里巧妙的使用一個enum當(dāng)工廠類的實現(xiàn)。整個代碼用了工廠模式加策略模式的實現(xiàn)。
優(yōu)點:得宜于lamdb的應(yīng)用,減少了具體工廠類的實現(xiàn)。
缺點:工廠模式可以實現(xiàn)不改動程序創(chuàng)建產(chǎn)品。那么這里如果要增一個產(chǎn)品,對這個enum類需要再添加一個枚舉變量。
這個enum類有改動。
]]>
https://github.com/daoqidelv/community-ddd-demo.git
作者不是俺!
]]>
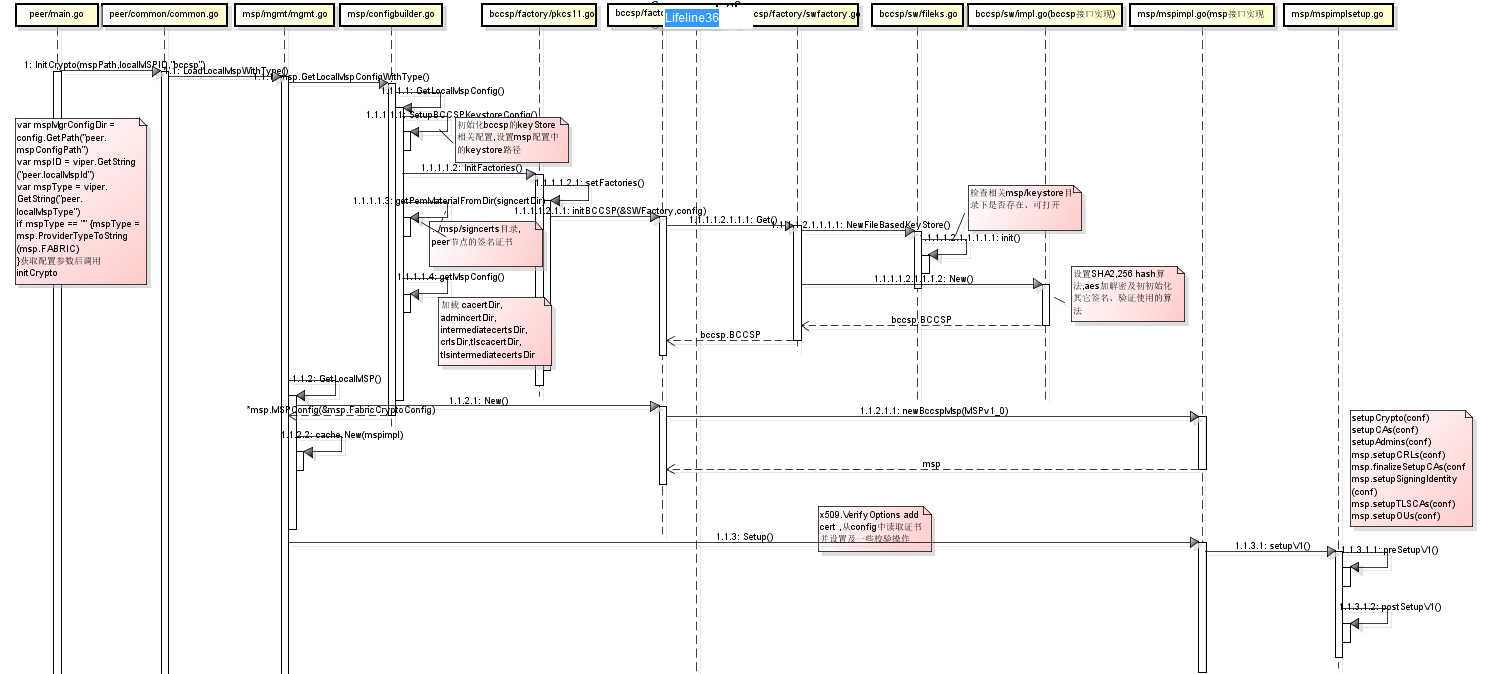
(MSP)是一個提供虛擬成員操作的管理框架的組件。
MSP抽取出簽發(fā)和驗證證書以及用戶認(rèn)證背后的所有加密機制和協(xié)議。 MSP可以定義自己的身份概念,以及這些身份管理的規(guī)則(身份驗證)和身份驗證(簽名生成和驗證)。
]]>
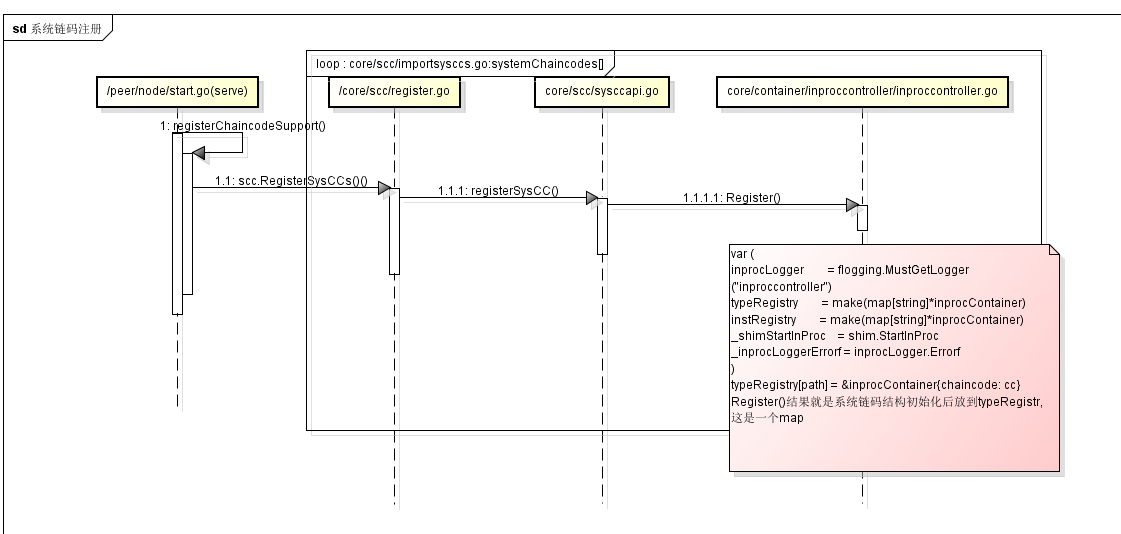
系統(tǒng)鏈碼初始化過程,可以找到../shim/handler.go中

]]>
* 鏈碼這一塊的代碼非常的繞。基本上就是一個大循環(huán)。限于水平或者其它原因,差露可能難免,各位看官包涵則個...

]]>
]]>
orderer start
2, 使用開發(fā)模式啟動peer節(jié)點
peer node start --peer-chaincodedev=true
3,創(chuàng)建通道
4,啟動鏈碼程序
這一步可以在IDE里啟動鏈碼,這樣就可以debug了
5,安裝鏈碼
6,初始化鏈碼
7,鏈碼調(diào)用和測試
]]>
準(zhǔn)備工作:(自行百度)
開發(fā)環(huán)境必備軟件:
composer-cli
generator-hyperledger-composr
composer-rest-server
Yeoman
安裝playground
docker ps -aq | xargs docker rm -f
docker images -aq | xargs docker rmi -f
curl -sSL https://hyperledger.github.io/composer/install-hlfv1.sh | bash

1,playground 的Web Browser區(qū)域提供了在頁面定義模型、測試模型的能力。并不保存。但可以導(dǎo)出bna文件
2,connection區(qū)域提供了在開發(fā)環(huán)境布署合約,會生成一個智能合約的docker運行環(huán)境.
3,可以在上圖中上部分的My Business Networks 工作區(qū)點擊虛業(yè)部分Deploy a new business network
4,在接下來頁面中選中一個示例。如 marble neetworkd. 選擇 ID and Secret 填入admin 和 adminpw
5,點擊Deploy按鈕后會發(fā)布一個合約.并跳到測試頁如下圖:
6,在上圖中 Test Tab頁可以進(jìn)行測試 ,在Define Tab頁可以導(dǎo)出bna文件.
7,在第一幅圖中點擊下載按鈕,會下載一個 .card文件,描述了連接fabric peer節(jié)點等相關(guān)連接信息.記得要導(dǎo) PeerAdmin@hlfv1的card和你自己測試用的card,及bna文件
8,分別執(zhí)行 composer card import -f PeerAdmin.card ,composer card import -f admin.card .composer card list 可以查看你導(dǎo)入的card的name信息.
9,composer-rest-server -c admin@empty-business-network -n always -w true 啟動rest服務(wù)默認(rèn)端口3000.
10,好了,可以體驗一下fabric是個什么玩意了。:) 88!
F{G7`1~XT5F5R]B$Q~T3P.png)
]]>
在閱讀本篇之前需要理解
如果知道通過命令行工具進(jìn)行智能合約的安裝測試就更好了。fabric中的channel可以理解為泳道。在這個泳道中可以布署
多個智能合約。當(dāng)然也可以安裝多個channel. 順便多一嘴,在智能合約可以調(diào)用另一個channel中的智能合約中的查詢方法.
通過sdk動態(tài)安裝通道的步驟:
1,通過configtxgen命令生成交易通道初始文件.
configtxgen --profile TestSoft --outputCreateChannelTx testsoft.tx --channelID testsoft
2,下載testsoft.tx到本機.
3,sdk安裝通道代碼及解釋
//初始化 ChannelConfiguration 對象.參數(shù)是通道初始化文件路徑
//構(gòu)造peer節(jié)點信息,并且將peer節(jié)點加入到通道中。peer節(jié)點加入通道后,才能通過該peer節(jié)點中訪問通道中的智能合約
知道了手工命令行安裝合約的過程,上面的理解還是比較簡單的。安裝通道后就可以調(diào)用sdk安裝合約了。
]]>
閱讀本代碼前,先看看fabric的多機布署,參考下面的貼子1:
參考貼子2: http://www.cnblogs.com/aberic/p/8206551.html ,把代碼下到本地工程里。新手上路總會遇到
各種細(xì)節(jié)問題.重點來了:
使用git命令從github.com上拉下SDK-JAVA源碼.
1,源碼文件中有EclipseSetup.md的文件,介紹如何把源碼項目導(dǎo)入eclipse.
2,導(dǎo)入eclipse后發(fā)現(xiàn)缺少 org.hyperledger.fabric.protos.*文件。github上的源碼里也沒有。解決辦法:從
其它網(wǎng)站的 SDK-JAVA打包文件中找到源碼包,把org.hyperledger.fabric.protos包中的源碼copy到eclipse。
3,在orderer節(jié)點把 crypto-config文件夾中的內(nèi)容copy到本機.其中包含了用命令工具生成的證書,身份信息
等內(nèi)容
4,貼子2中代碼如何用,其實跟源碼中的測試用例中的代碼差不多.初始化示例如下:因為貼子2是個demo類代碼,
我作了些改動。有些代碼沒放ChaincodeManager()實例化。看一下這個類的構(gòu)造方法,構(gòu)造對應(yīng)的需要的實例類
也不難
//crypto-config文件夾
5,其它參數(shù),比如chaincode相關(guān)信息可以在peer節(jié)點 peer chaincode list --installed 命令可以查看
可以調(diào)用這個ChaincodeManager 的query和invoke方法了.
6,補充內(nèi)容:需要shim-client.jar包,這個需要拉下fabric的源碼,在文件夾
\src\github.com\hyperledger\fabric\core\chaincode\shim\java 用gradle編譯一個jar包出來
7,如果grpc用了ssl的需要 grpcs://10.121.60.3:7051,grpcs開頭
因為網(wǎng)上有了fabric多機布署教程,和不完善的示例代碼,這里主要介紹一下其中容易遇到的問題,解決起
來也頗為頭痛和費時。
本貼原地址:http://www.tkk7.com/fool .下一篇區(qū)塊鏈貼子預(yù)告:Fabric的SDK-JAVA動態(tài)安裝
Channel
]]>
2,logstash/config目錄下新建log.conf文件,其內(nèi)容:
3,kibana配置.修改kibana/config文件夾中的kibana.yml的配置文件
4,springCload、springBoot中的logback-spring.xml文件配置將日志寫入logstash
后記:日志是直接寫入到elashticsearch,可以集成kafka或redis作為緩沖。
]]>
]]>
定義參數(shù)解析器來綁定參數(shù),通過它可以拿到ServletRequest中的attirbute中的值進(jìn)行參數(shù)
綁定。
自定義一個annotation,通過這個注解中的 name查找attribute中的key對應(yīng)的值
springboot中注冊自定義的參數(shù)解析器
}
使用方法.
需要在action調(diào)用前向HttpServletRequest中的attribute中注入值 ,可以自定義一個filter,在filter中進(jìn)行處理
如在filter中處理app傳過來的token驗證后取得對應(yīng)的用戶信息等.下面例子簡單放入一個對象
action獲取attribute中放入的對象
嗯,還算優(yōu)雅
]]>
任務(wù)類或方法
]]>
@Bean
2,攔截器
不執(zhí)行,那么只能在preHandle中處理了,比如轉(zhuǎn)向,ajax請求返回內(nèi)容
3,關(guān)于快速跳轉(zhuǎn)
有時候只是做一個簡單的跳轉(zhuǎn),可以集中寫在這里
完整示例:
文件上傳控制器類
]]>
寫配置類配置jsp支持
}
所謂零配置。。。 一言難盡
]]>
頁面中angularjs展示數(shù)據(jù)
<body ng-controller="multi">
<tbody>
<tr ng-repeat="item in defaultData " >
<td class='center hidden-480'>{{item.title}}</td>
</body>
</table>
</body>
外部jquery的ajax調(diào)用更新數(shù)據(jù)
<tr ng-repeat="item in defaultData " >
]]>
維護(hù),規(guī)則名稱編號可以與用例名稱編對一一對應(yīng)。
業(yè)務(wù)規(guī)則分類:
一,內(nèi)稟規(guī)則:業(yè)務(wù)實體本身的規(guī)則。如訂單中銷售記錄不能為空,數(shù)量不能為等。
二,全局規(guī)則:一般與所有用例相關(guān)而不是某個特定用例相關(guān)。例如系統(tǒng)安全方面的sql注入,ddos攻擊等。
三,交互規(guī)則:用于用例當(dāng)中。它們規(guī)定了滿足什么條件后業(yè)務(wù)將如何反應(yīng)。有些規(guī)則需要開發(fā)成系統(tǒng)用例。比如人事
管理系統(tǒng)中請假業(yè)務(wù)只有工作日才計入請假天數(shù),那么這個工作日就需要電腦來維護(hù)了,會作為一個系統(tǒng)用例存在,并
且作為請假用例的前置條件。 交互規(guī)則又是最容易引起.
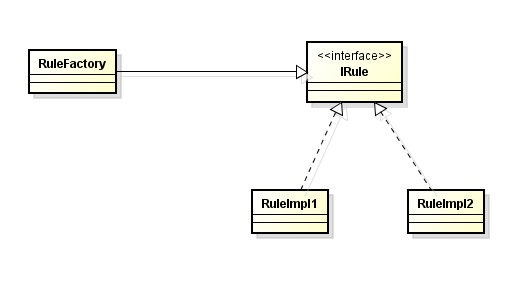
交互規(guī)則如此靈活多變,需要良好的設(shè)計才能保證系統(tǒng)的擴展性和可維護(hù)性。如何做:
思路一:
在 javax.swing.border包提供了Border接口和幾個不同的Boder的實現(xiàn)。在swing中每個組件提供了paint方法,每
個組件知道怎么畫自己展示自己的外觀。那么我們可以提供業(yè)務(wù)規(guī)則處理接口,每個具體業(yè)務(wù)規(guī)則自己知道怎么處理業(yè)務(wù)。
可以用簡單工廠來決定調(diào)用哪一個具體業(yè)務(wù)規(guī)則。這個是策略模式的使用,缺點是新增具體業(yè)務(wù)時工廠類會修改。也可以
用觀察者模式來實現(xiàn),所有的具體業(yè)務(wù)類都來觀察這個業(yè)務(wù)規(guī)則,自己判斷是不是自己可以處理的,不是就不理會。
基于策略模式的規(guī)則實現(xiàn)類圖:
思路二:
規(guī)則引擎比如drools處理一些問題 。規(guī)則引擎適合于做業(yè)務(wù)規(guī)則頻繁變化的場景.把業(yè)務(wù)規(guī)則抽出來通過規(guī)則引擎來
處理。類似工作流系統(tǒng)的概念。
自定義規(guī)則處理庫:
一些動態(tài)的語言很適合來做這樣的事情。java支持script.Mvel是一個表達(dá)式語言,drools也支持mvel來處理業(yè)務(wù)規(guī)則.
這里自定義規(guī)則引擎使用Mvel表達(dá)式語言.
規(guī)則文件示例:
<rules>
本例依賴xstream1.4.9 ,mvel2.0
自定義規(guī)則庫除了可以應(yīng)用于一般系統(tǒng)業(yè)務(wù)處理,當(dāng)然也還可以用于大數(shù)據(jù)處理。比如hadoop/spark統(tǒng)計用戶積分等
如果再定義一套配置規(guī)則的UI。。。好的,業(yè)務(wù)人員可以自己設(shè)置計算規(guī)則了。
]]>
一,需求收集,分析。
此處省略2000字。。。 見前篇 《需求收集、分析小結(jié)》http://www.tkk7.com/fool/archive/2017/04/28/432489.html
二,概念架構(gòu)/概念模型
從需求中找出關(guān)健、重大需求,進(jìn)行概念建模.下面三個圖稱之魯棒圖。其中控制對象理解為mvc模式中的控制器和model。使用魯棒圖可以建立概念模型,約等于初步設(shè)計。初步設(shè)計并不關(guān)心細(xì)節(jié)。

魯棒圖建立概念模型語法: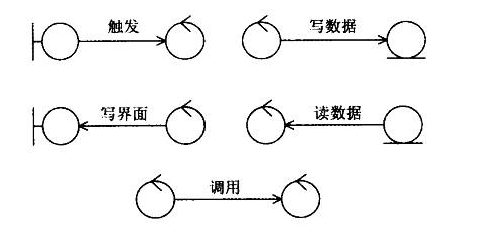
概念設(shè)計舉例:
上次談到超市小票如何分析實體對象,本次接著舉例如何對收銀進(jìn)行概念建模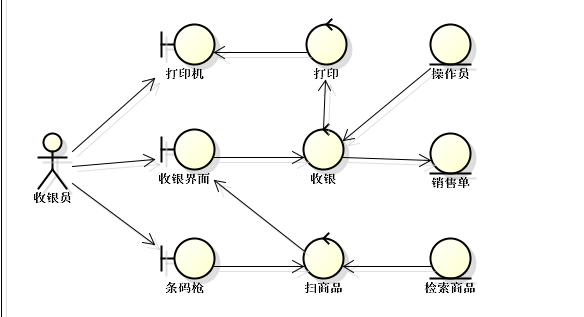
如上圖:具備基本收銀功能的概念模型。概念模型建模可以是增量的。比如商品折扣或其它
促銷活動等。
概念架構(gòu)的用途:
1) 可以幫助我們找出領(lǐng)域模型中的實體對象。
2) 檢查需求用例是否正確和完善。
3)初步設(shè)計,魯棒圖是一種初步設(shè)計技術(shù)。
4)根據(jù)用例和概念設(shè)計劃分系統(tǒng)、子系統(tǒng)、模塊或者包。借助魯棒圖,初步識別功能背后的職責(zé),規(guī)劃切分系統(tǒng)的方式。
三,關(guān)注非功能性需求,包括運行期質(zhì)量和開發(fā)期質(zhì)量。
運用目標(biāo)—場景—決策表對非功能性需求作出決策.小舉例:
| 目標(biāo) | 場景 | 決策 |
| 易用性 | 銷售員需要輸入條碼檢索商品,繁瑣且速度慢 | 根據(jù)條碼,品名模糊匹配檢索商品,提供輔助錄入。 |
| 性能 | 長時間穩(wěn)定運行 | 數(shù)據(jù)庫集群,服務(wù)應(yīng)用集群 |
度快
四,細(xì)化架構(gòu)。RUP 4+1視圖法則將架構(gòu)需要關(guān)注的不同的點使用不同的視圖表示.從不同的維度對系統(tǒng)進(jìn)行解讀,從而形成統(tǒng)一軟件過程架構(gòu)描述。
運行架構(gòu):
關(guān)心進(jìn)程、線程、同步的相關(guān)設(shè)計,捕捉并發(fā)和同步特征
邏輯架構(gòu):
關(guān)心邏輯層(layer)的劃分,系統(tǒng)/子系統(tǒng)的劃分,劃分模塊及其接口的定義。功能組劃分也屬于邏輯架構(gòu).功能:不僅包括用戶可見的功能,還包括為實現(xiàn)用戶功能而必須提供的"輔助功能模塊";它們可能是邏輯層、功能模塊等。
物理架構(gòu):
關(guān)心服務(wù)器選型,物理層劃分(tier)。 描述如何部署機器和網(wǎng)絡(luò)來配合軟件系統(tǒng)的可靠性、可伸縮性等要求.layer就運行在tier上。Tier反映系統(tǒng)伸縮能力。
開發(fā)架構(gòu):
描述了在開發(fā)環(huán)境中軟件的靜態(tài)組織結(jié)構(gòu)。即開發(fā)工具下的開發(fā)視圖,描述文件編譯及其依賴關(guān)系。而使用maven管理開發(fā)的項目編譯及依賴關(guān)系結(jié)構(gòu)更加分明。
數(shù)據(jù)架構(gòu):
關(guān)心數(shù)據(jù)的存儲、分布和文件的存放及數(shù)據(jù)的復(fù)制,傳遞,同步。數(shù)據(jù)的存放包括sql,內(nèi)存數(shù)據(jù)庫,nosql數(shù)據(jù)庫等.
邏輯架構(gòu)設(shè)計舉例:
還是用收銀系統(tǒng)簡單舉例,收銀系統(tǒng)邏輯架構(gòu)圖如下: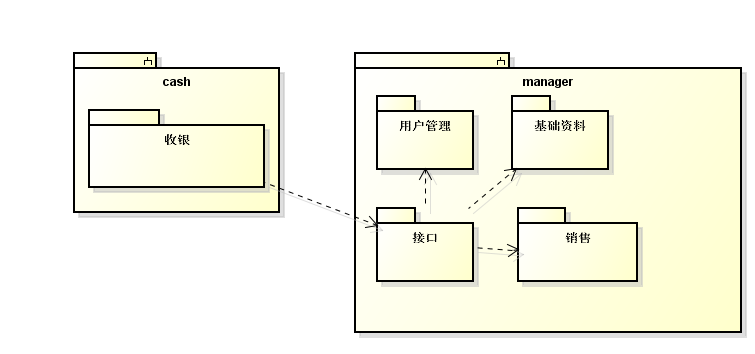
整個系統(tǒng)劃系統(tǒng)為系統(tǒng),切為兩個系統(tǒng),一個收銀員角色處理的業(yè)務(wù),收銀系統(tǒng)。
一個后臺管理系統(tǒng)。后臺管理系統(tǒng)包括用戶管理模塊,基礎(chǔ)資料模塊(產(chǎn)品資料等)
銷售模塊(本例對銷售單)。另外,因為收銀系統(tǒng)需要和后臺系統(tǒng)交互,把收銀系統(tǒng)需要使用到的相關(guān)的各模塊封裝成一個接口模塊,專門處理和收銀系統(tǒng)交互的模塊。系統(tǒng)、模塊之間的通訊方式應(yīng)當(dāng)盡量避免雙向。相互依賴可能會引發(fā)很多問題。
物理架構(gòu)設(shè)計舉例:
物理架構(gòu)和邏輯架構(gòu)可以相互印證。描述軟件系統(tǒng)的物理布署。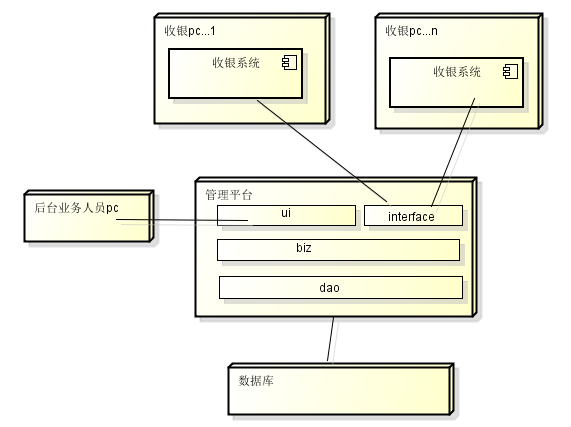
如果考慮運行期質(zhì)量比如長時間運行布署圖可能應(yīng)用做集群。數(shù)據(jù)庫做集群等。邏輯層layer運行在物理層tier之上
運行架構(gòu)和數(shù)據(jù)架構(gòu)視圖根據(jù)實際情況可選設(shè)計
]]>